The universal read-only APIs for enterprise directories
Modern apps should not have to speak LDAP.
Universal Directory Sync absorbs the fragile parts of directory integration so your apps can read a dependable data feed.
01
Certificate friction
LDAPS on port 636 breaks when app runtimes cannot trust the AD certificate chain.
02
Stateful connections
Lambda and serverless jobs are poor homes for long-lived directory connections.
03
Credential exposure
Bind passwords end up in scripts, logs, and local configs when every app rolls its own sync.
04
IAM-suite pricing
Bind passwords end up in scripts, logs, and local configs when every app rolls its own sync.
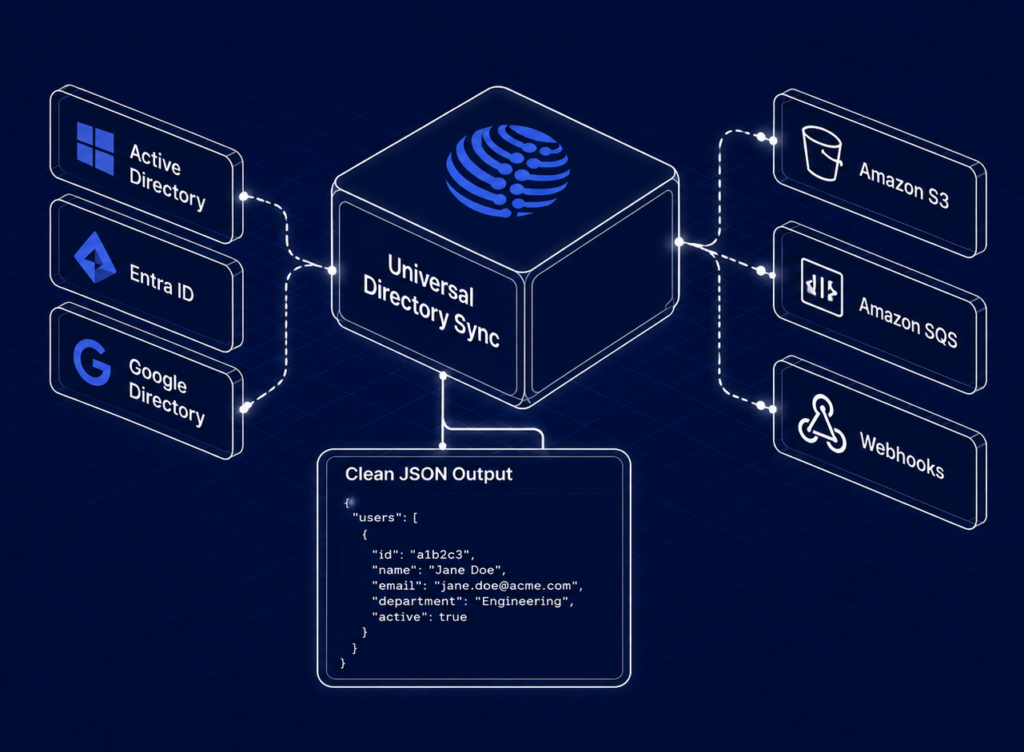
From directory tree to AWS-native data stream.
Configure once, preview output, then deliver clean identity data wherever your stack needs it.
Connect a source
Preview safely
Simulation mode shows mappings, counts, and proposed changes before anything ships.
Choose sinks
Send snapshots to S3, change events to SQS, and targeted updates to Webhooks.
Set frequency
Monthly for labs, daily for production, or event-driven sync for provisioning flows.
Consume JSON
Power Lambda functions, internal tools, HR dashboards, audits, and AI workflows.
Data lands where your team already works.
Choose durable snapshots, reliable events, or real-time pushes without adding a new data platform.

Versioned JSON snapshots for audits, dashboards, search, and downstream jobs.
s3://identity/users-latest.json

At-least-once change events for provisioning, deprovisioning, and retries.
{"event":"user.updated"}

HTTP posts to Retool, Appsmith, n8n, or a custom endpoint outside AWS.
POST /api/identity-sync
From directory tree to AWS-native data stream.
Configure once, preview output, then deliver clean identity data wherever your stack needs it.
Product
Model
Output
Universal Directory Sync
Per connection
S3, SQS, Webhooks
Auth0 / Okta
Per user
No native S3/SQS
WorkOS
Per connection
SCIM-focused
Custom ETL
Build yourself
Manual pipelineSCIM-focused
Enterprise controls,
packaged for developer workflows.
Secrets Manager
Bind credentials are encrypted and rotated without application code changes.
Least privilege
Read-only sync accounts and scoped organizational units by default.
End-to-end encryption
TLS 1.3 in transit, AES-256 at rest, and CA certificate upload for LDAPS.
Audit logging
Every add, update, delete, and failure is captured for operational review.
PrivateLink
Enterprise plans keep LDAP traffic off the public internet.
Safety switch
Syncs pause when proposed changes exceed the configured threshold.
No SSO tax.
No per-user surprises.
The Lab
$0/mo
For developers validating mappings and building proofs of concept.
- 1 directory connection
- Monthly sync
- Up to 250 records
- S3 and Webhook sinks
Standard
$125/mo
Production sync for startups and SMBs without enterprise spend.
- Daily sync
- Up to 10,000 records
- S3, SQS, and Webhooks
- Email support
Real-Time
$200/mo
Event-driven sync for automated provisioning workflows.
- On-demand sync
- Up to 25,000 records
- EventBridge ready
- Priority support
Enterprise
Custom
Private networking, dedicated SLAs, and procurement support.
- Unlimited connections
- AWS PrivateLink
- 99.9% SLA
- Dedicated success
The final objections,
answered fast.
Does Universal Directory Sync store my directory data?
No. It processes directory data and writes it to infrastructure you own, such as your S3 bucket or SQS queue.
What sources are supported?
Microsoft Active Directory, Microsoft Entra ID, Google Directory, OpenLDAP, and standard LDAPv3 servers.
How is this different from AWS AD Connector?
AD Connector redirects authentication. Universal Directory Sync exports normalized JSON data for apps and workflows.
Can teams buy through AWS Marketplace?
Yes. Standard, Real-Time, and Enterprise procurement can align with AWS Marketplace billing.